<Hello World!/>
I am
#Akhil Jose
I specialise in Cybersecurity Operations | Vulnerability Management | Threat Intelligence/>

About me/>
In the vast cosmos of life’s possibilities, I have always been the stargazer, the seeker of answers, and the relentless explorer. Like a child gazing at the night sky, pondering the mysteries of the cosmos, I’ve always asked, “Who am I?” This insatiable curiosity has been my guiding star throughout my life, propelling me towards uncharted territories and pushing the boundaries of my capabilities.
Cat cosmos.sh
My journey has been anything but conventional. From the esoteric realms of philosophical inquiry to the artistry of filmmaking, I’ve ventured down diverse paths, all fueled by an unquenchable thirst for knowledge. However, it was during my foray into web design and development that I stumbled upon a realm that would become my true passion: cybersecurity.
Cat cybersecurity.sh
Cybersecurity, for me, is not just a profession; it’s a calling. It’s the realm where my curiosity meets its match, where I found my purpose in safeguarding the digital world. As I ventured deeper into this dynamic field, I began to assist organizations in fortifying their digital defenses.
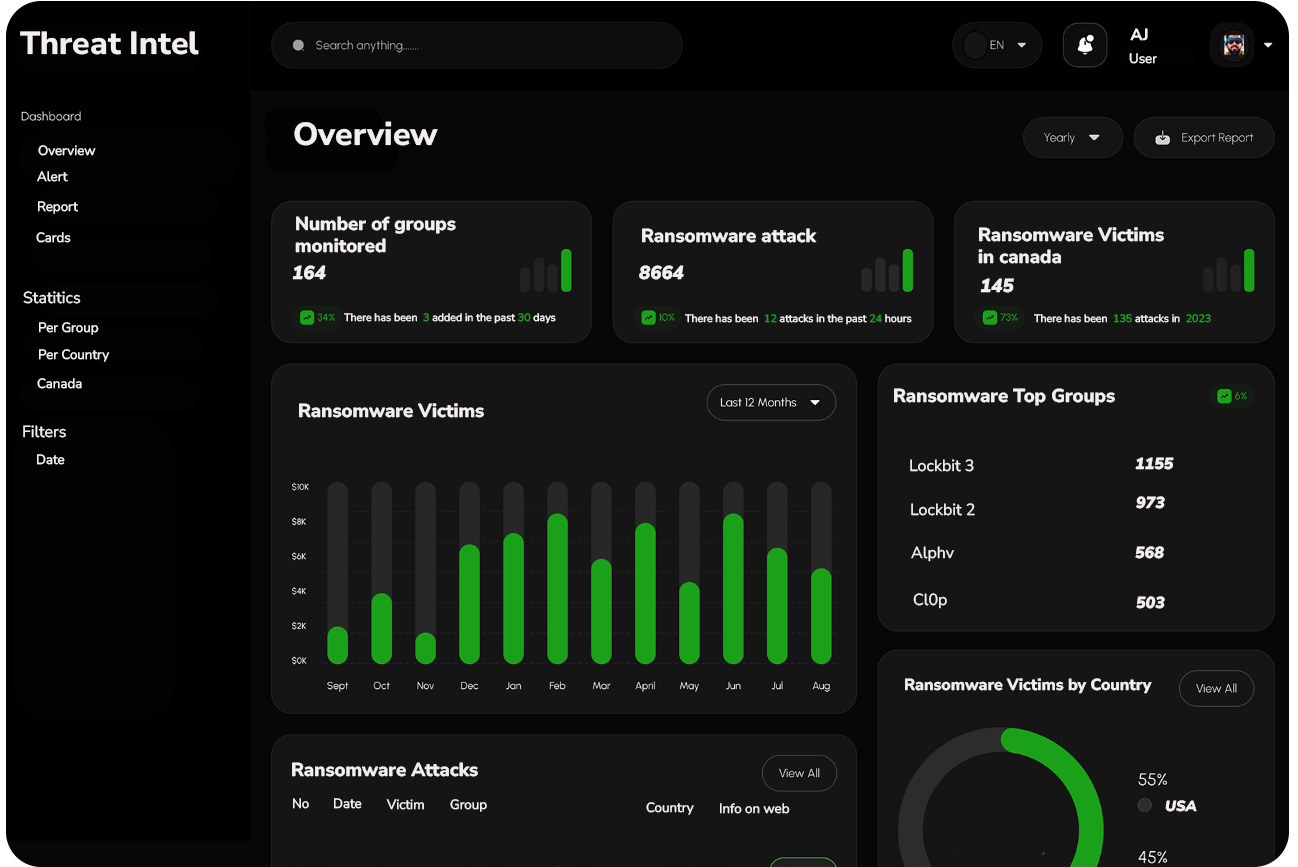
My academic journey at York University further enriched my understanding, equipping me with skills in Threat Intelligence, digital forensics, and incident response. Here, I even undertook the audacious challenge of constructing a threat intelligence framework to monitor the dark web, a journey that took me to the uncharted depths of cyber threat hunting.
My philosophy has always revolved around continuous improvement. I firmly believe that even the best can be made better.
Profile/>
Projects/>
Darweb Monitoring tool
Live
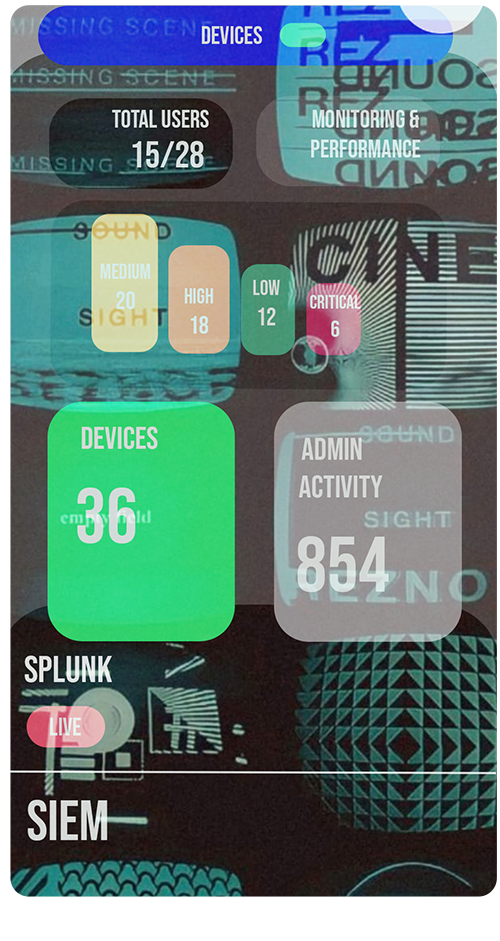
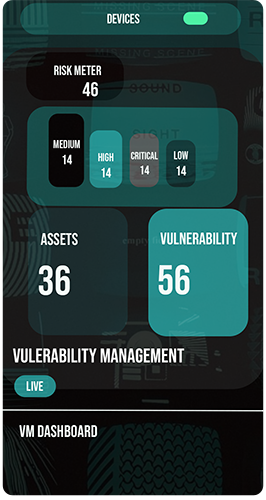
Vulnerability Management/>
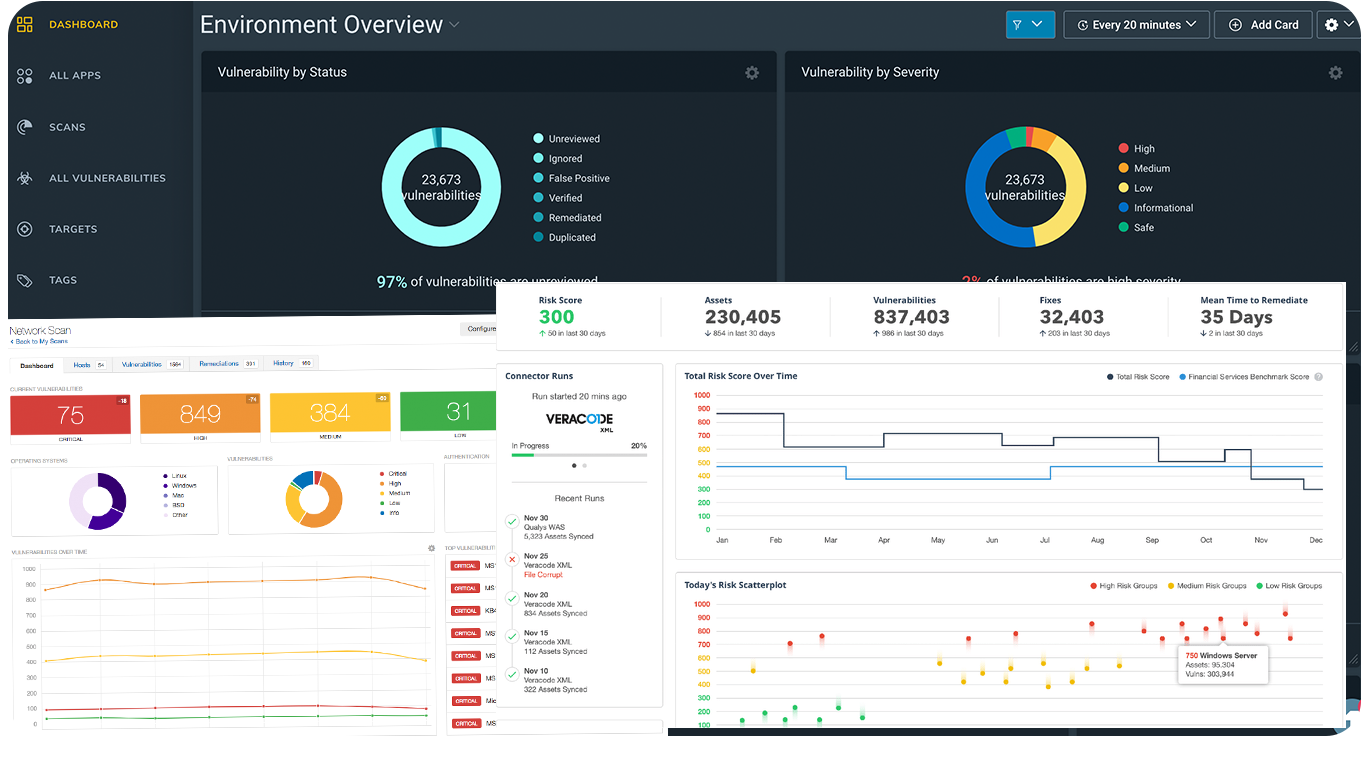
In my captivating digital journey, I’ve had the privilege of utilizing powerful tools that have revolutionized my perspective. Picture me immersing myself in the realm of cybersecurity, armed with the likes of Rapid7 Nexpose, Microsoft Defeeder, Nessus, OpenVas, Cisco-Kenna, NIST, ISO standards, and more. These tools have become my trusted allies, equipping me to navigate the intricate landscapes of vulnerability assessment and risk management. With each scan and analysis, I uncover hidden vulnerabilities, reinforce defenses, and safeguard digital environments. But my journey doesn’t end there. To enhance my insights, I harness the power of Python and Pandas to generate comprehensive reports and perform in-depth analysis. The data derived from these analyses is then fed into an intuitive dashboard for further exploration and interpretation. It’s a thrilling adventure that keeps me constantly on my toes, eager to push the boundaries of knowledge in the ever-evolving world of cybersecurity.
Live
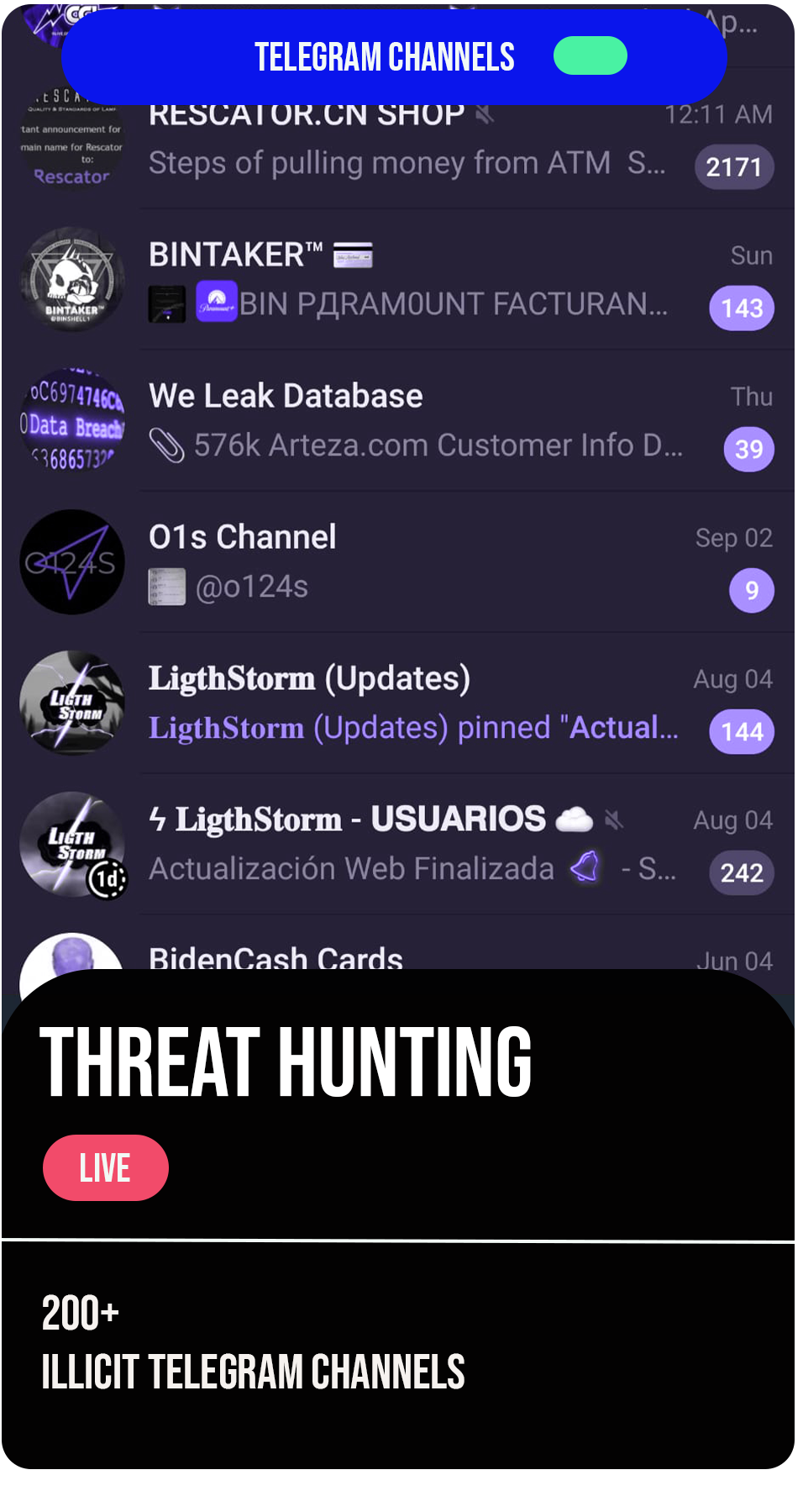
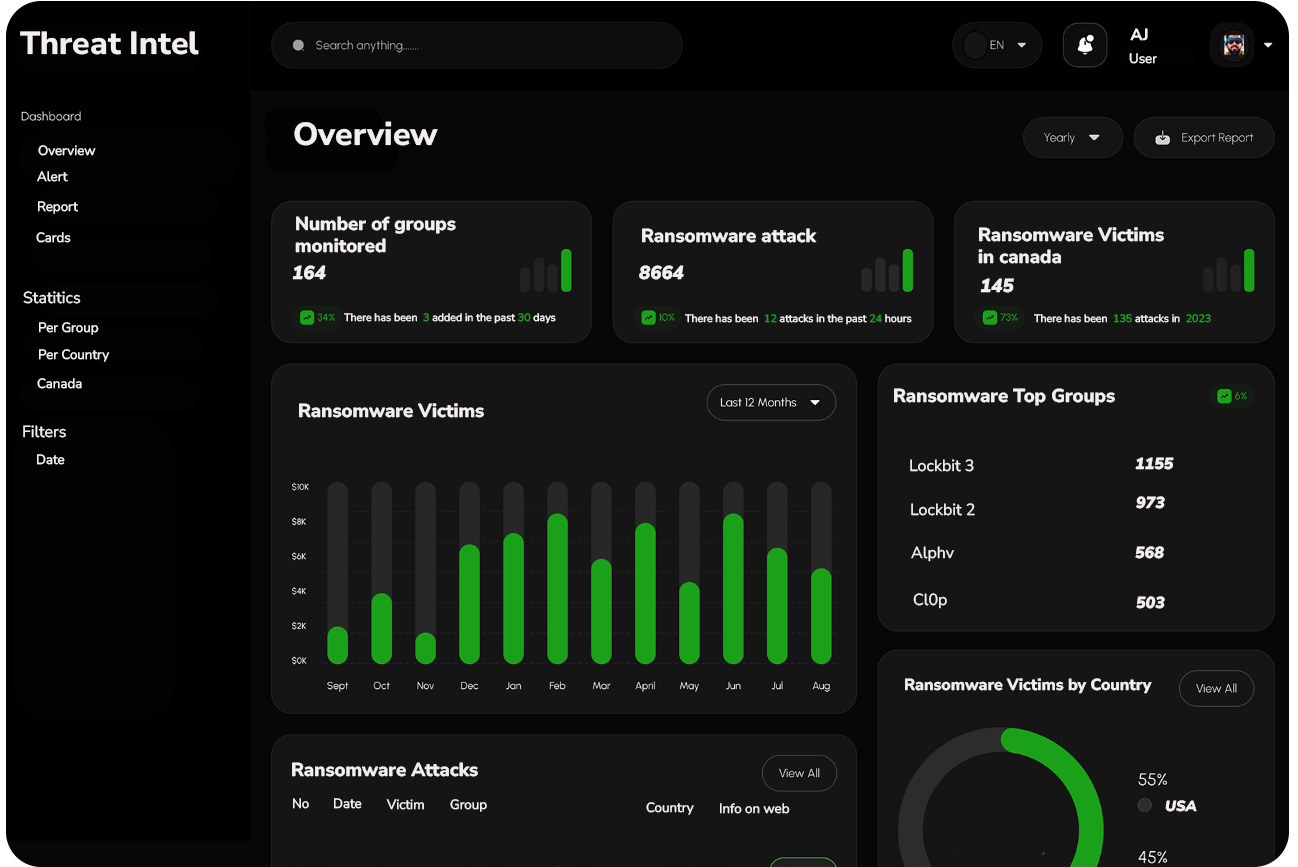
Threat Intelligence/>
In the dynamic realm of threat intelligence, I’ve had the opportunity to harness an array of powerful tools that have reshaped my understanding. Imagine immersing yourself in the intricacies of cybersecurity, armed with Mandiant Advantage for proactive monitoring. This invaluable tool has become my steadfast companion, enabling me to stay ahead of emerging threats and swiftly respond to potential breaches. But my journey doesn’t end there. To enhance my capabilities, I’ve developed a framework for adhoc scanning, leveraging OSINT (Open Source Intelligence), feeds, and other resources for proactive threat hunting. This comprehensive approach keeps me constantly updated and prepared in the ever-evolving field of cybersecurity. It’s an exhilarating quest that fuels my passion to conquer new frontiers and safeguard digital environments from malicious actors.
Digital Forensics/>
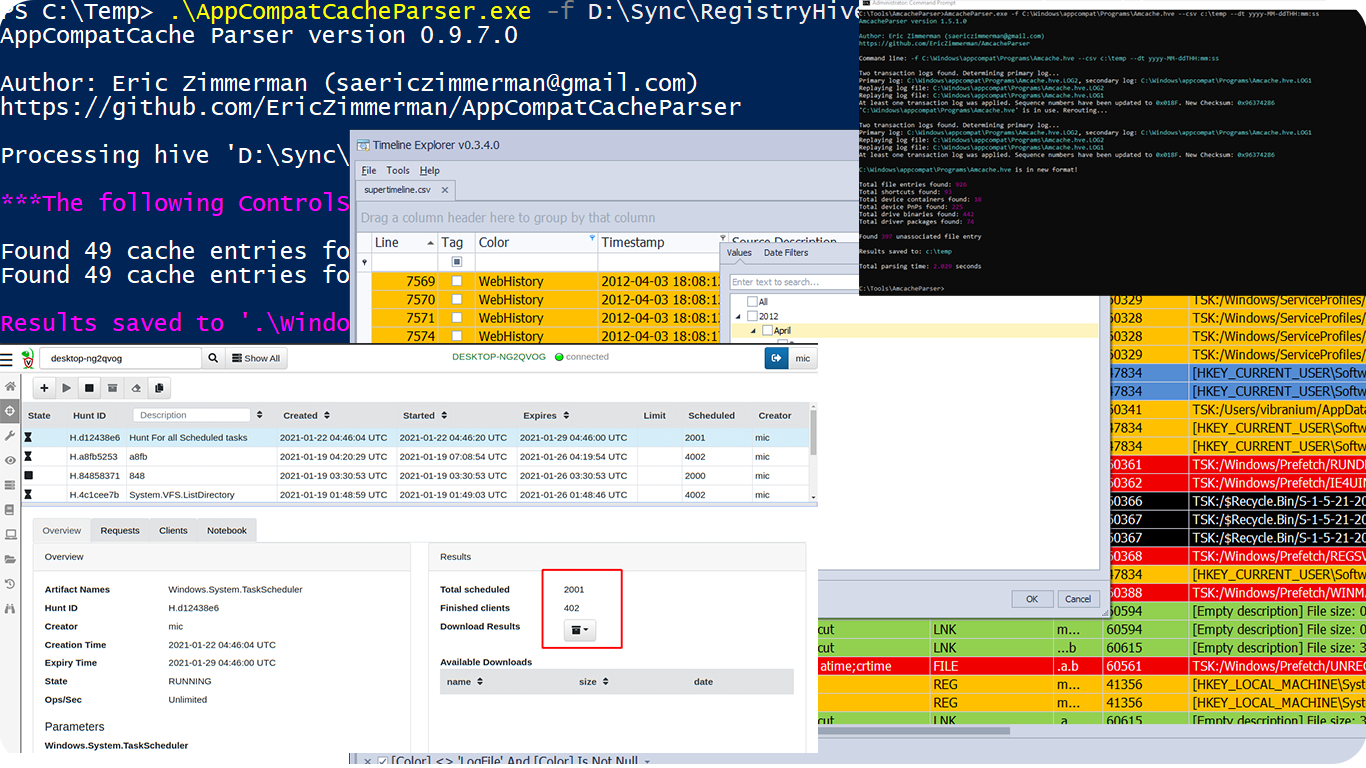
When I thought my digital forensic journey couldn’t get any more thrilling, I embarked on a course that introduced me to a fascinating arsenal of tools. These digital forensic tools are like secret weapons, enabling investigators, law enforcement agencies, and skilled professionals to collect, analyze, and safeguard crucial digital evidence from electronic devices. Picture yourself wielding the power of Velociraptor, Eric Zimmerman’s EZ Tools, DD, FTK Images, Volatility, EZparser, Timeline Viewer, Hex Editor, PE Studio, Cyber Chef, Sigma, and Achunter. It’s like stepping into a realm of limitless possibilities, where you uncover hidden truths and expose cybercrime. I’m so engrossed in this world that I devour podcasts, follow blogs, and even create scripts. The latest conquest? Converting OSC to PST It was an exhilarating journey that left me craving more.
Live
Cybersecurity Operations/>
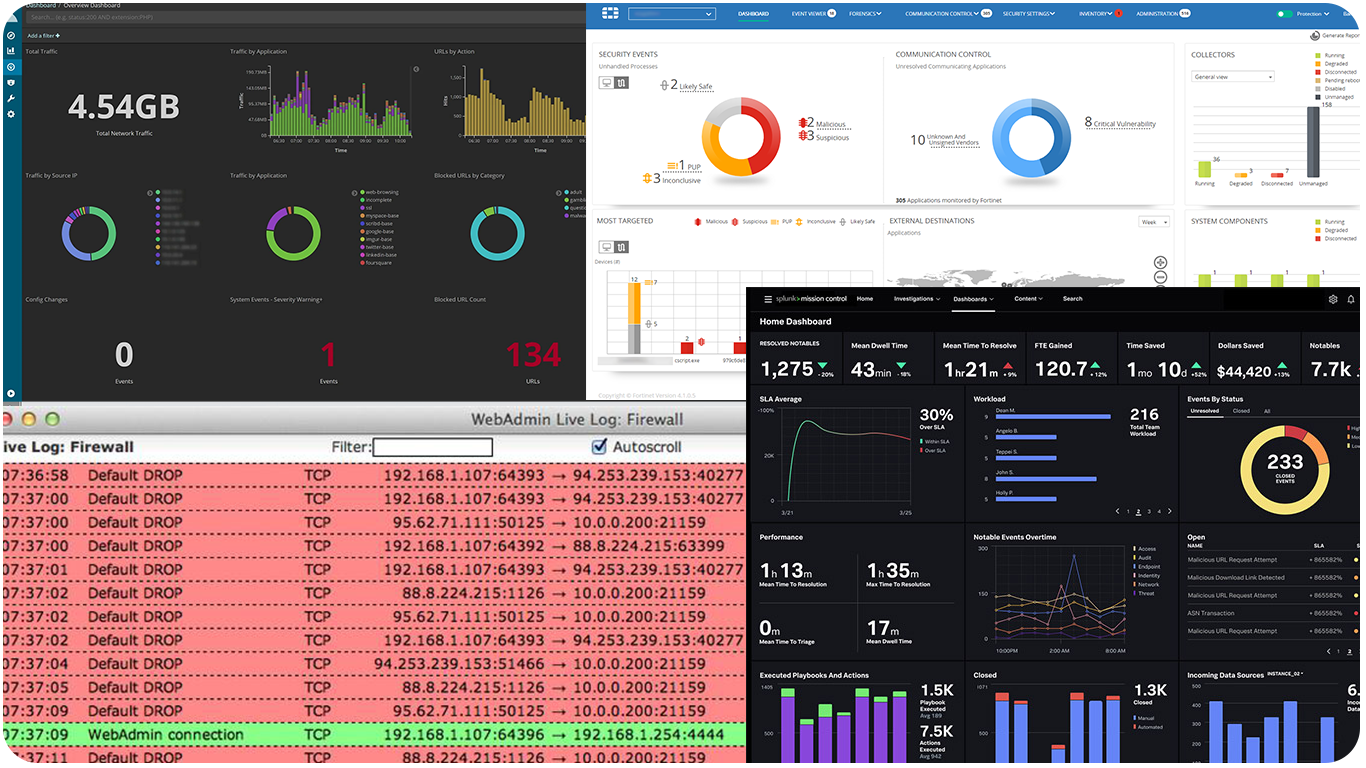
In the world of cybersecurity operations and incident response, I’ve utilized powerful tools like Splunk, Sentinel EDR, and Fortiedr to enhance my understanding. With OSINT , I proactively monitor and swiftly respond to emerging threats and potential breaches. Additionally, I’ve developed a framework for proactive threat hunting, using OSINT, feeds, and other resources to stay updated and prepared. This comprehensive approach keeps me at the forefront of cybersecurity. It’s an exciting journey that drives my passion to protect digital environments from malicious actors and conquer new challenges.
Get In Touch/>

Contact Info
Toronto, On
Canada
Contact Info
+1 519-722-2321
akhil.jose@lowsage.com